Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
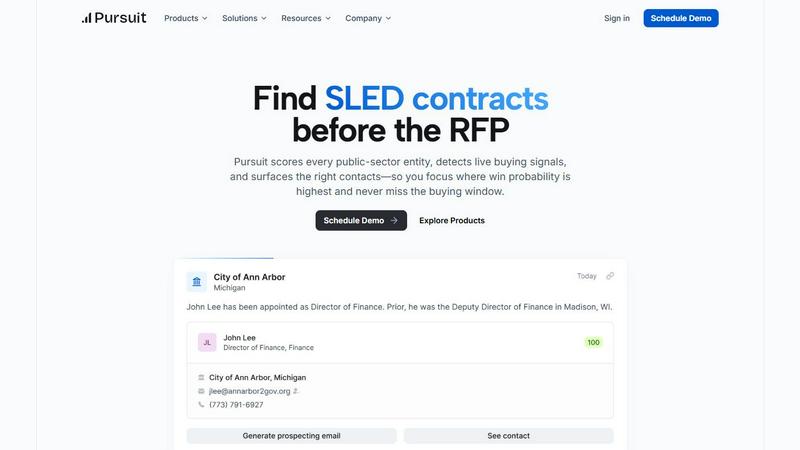
Pursuit
Pursuit uncovers buying signals from public sector agencies up to 18 months early, helping you win SLED deals.
Last updated: February 28, 2026
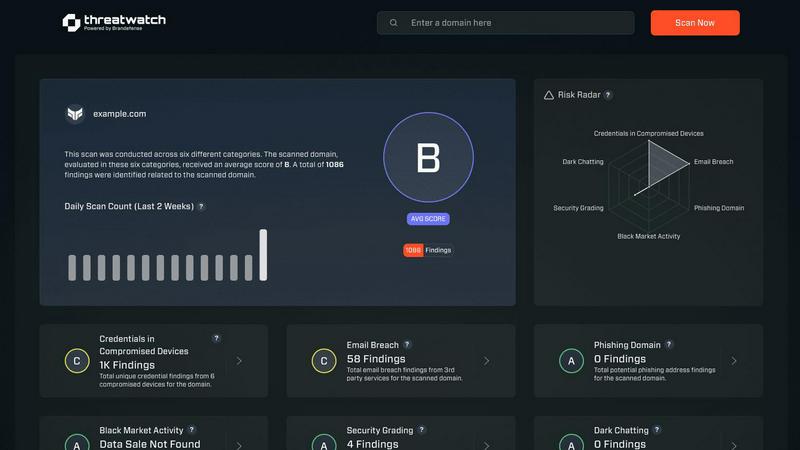
Threat Watch
Quickly assess your cybersecurity health with Threat Watch's insights on compromised accounts and potential threats.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Intelligence
Pursuit surfaces buying signals 6 to 18 months prior to RFPs being released. This foresight ensures that your sales team is positioned as the incumbent, allowing you to build relationships and trust before the formal procurement process begins.
Continuous Data Monitoring
The platform continuously analyzes data from a vast array of public entities, ensuring that the insights are timely and relevant. This feature allows sales teams to stay ahead of market trends and procurement cycles, making informed decisions that enhance their strategic approach.
Native Integrations
Pursuit offers seamless integration with popular CRM solutions such as Salesforce and HubSpot. This ensures that data flows directly into your existing tech stack, enabling your teams to work efficiently without the need for extensive engineering resources.
Comprehensive Signal Analysis
With its advanced algorithms, Pursuit detects live buying signals from various documents and meetings. This feature provides users with actionable insights into when and how to engage with potential clients, significantly increasing the likelihood of closing deals.
Threat Watch
Comprehensive Risk Assessment
Threat Watch provides a thorough evaluation of an organization’s cybersecurity posture by analyzing essential security categories. This feature allows users to identify potential weaknesses and prioritize remediation efforts based on the severity of identified risks.
Real-Time Insights
Stay ahead of cyber threats with Threat Watch's real-time insights. This feature continuously monitors the digital landscape, providing organizations with up-to-date information about emerging threats and vulnerabilities, enabling timely decision-making.
Automated Reporting
With advanced automation capabilities, Threat Watch generates detailed reports that summarize critical security findings. This feature streamlines the reporting process, making it easier for security teams to communicate risks and compliance status to stakeholders.
Dark Web Monitoring
Protect your organization's sensitive data with Threat Watch's dark web monitoring feature. This capability alerts users about compromised credentials and sensitive information that may be circulating on the dark web, allowing for swift action to secure assets.
Use Cases
Pursuit
Sales Enablement
Sales teams can leverage Pursuit to identify in-market accounts and prioritize outreach based on real-time buying signals. This proactive approach empowers reps to focus their efforts where they are most likely to win, rather than relying on cold outreach.
Account-Based Marketing (ABM)
Marketing professionals can create targeted ABM campaigns by utilizing insights from Pursuit, such as budget approvals and contract expirations. This ability allows for strategic audience segmentation and tailored marketing efforts that resonate with decision-makers.
Territory Management
Sales leaders can analyze territory coverage and identify gaps using Pursuit’s insights. By understanding which buying signals are being monitored, they can allocate resources more effectively and ensure that their teams are maximizing opportunities.
Customer Success Monitoring
Customer success teams can set configurable alerts for contract renewals and monitor for churn signals. By being notified of potential issues such as budget cuts or leadership changes, they can proactively engage clients to enhance retention and satisfaction.
Threat Watch
Identifying Vulnerabilities
Organizations can utilize Threat Watch to conduct regular assessments of their network and systems, identifying vulnerabilities before they can be exploited by cybercriminals. This proactive approach enhances overall security posture.
Incident Response Planning
In the event of a security incident, Threat Watch provides valuable intelligence that aids in incident response planning. Security teams can analyze compromised accounts and phishing attempts to develop strategies to mitigate future risks.
Cyber Hygiene Maintenance
Regular scans with Threat Watch help organizations maintain cyber hygiene by continuously monitoring for compromised credentials and vulnerabilities. This ongoing vigilance is essential for sustaining a secure digital environment.
Compliance Assurance
For organizations subject to regulatory requirements, Threat Watch assists in maintaining compliance by providing insights into security vulnerabilities and breaches. This feature ensures that businesses can demonstrate their commitment to cybersecurity best practices.
Overview
About Pursuit
Pursuit is an innovative AI-powered intelligence platform tailored specifically for businesses aiming to penetrate the often complex public sector market, particularly focusing on state, local, and educational (SLED) government entities. The core proposition of Pursuit is to transform the perception of the public sector from a bureaucratic maze into a landscape filled with actionable opportunities. By continuously monitoring and analyzing data from over 110,000 public entities, Pursuit provides critical insights into procurement cycles, budgeting processes, and key decision-makers, allowing sales teams to identify potential buyers long before formal Requests for Proposals (RFPs) are published. This proactive approach enables organizations to build relationships, capitalize on buying signals, and significantly enhance their success rates. Ultimately, Pursuit streamlines the sales process, reduces research time, and empowers teams to focus on high-probability opportunities, making it an essential tool for fast-growing government contractors and technology providers.
About Threat Watch
Threat Watch is a sophisticated cybersecurity intelligence solution designed to empower organizations by providing them with a clear understanding of their cyber health. This innovative tool meticulously evaluates a multitude of critical security categories, such as compromised credentials, breached accounts, phishing addresses, and dark web content. By presenting a unified view of an organization’s assets, vulnerabilities, and exposures, Threat Watch enables IT professionals, security teams, and business leaders to swiftly identify and prioritize risks. The main value proposition lies in its ability to transform complex data into actionable intelligence, allowing businesses to mitigate risks faster and more effectively than ever before. With real-time insights and automated assessments, organizations can proactively safeguard their digital environments. Discover your cybersecurity health and fortify your defenses with Threat Watch, a crucial ally in the evolving landscape of cybersecurity threats.
Frequently Asked Questions
Pursuit FAQ
How does Pursuit help with understanding the public sector procurement process?
Pursuit provides detailed insights into the unique procurement processes of over 110,000 public entities. By analyzing trends and historical data, it helps businesses navigate the complexities of public sector sales more effectively.
Can Pursuit integrate with existing CRM systems?
Yes, Pursuit offers native integrations with popular CRM platforms such as Salesforce and HubSpot. This ensures seamless data flow and operational efficiency without requiring extensive engineering efforts.
What types of buying signals does Pursuit analyze?
Pursuit analyzes various signals including budget approvals, leadership changes, contract expirations, and procurement documents. This comprehensive analysis allows sales teams to act on real-time opportunities.
How does Pursuit improve the efficiency of sales teams?
By providing actionable insights and prioritizing outreach based on buying signals, Pursuit reduces the time sales teams spend on research and cold outreach. This allows them to focus on high-probability opportunities, increasing win rates significantly.
Threat Watch FAQ
How does Threat Watch improve cybersecurity?
Threat Watch improves cybersecurity by providing real-time insights and automated assessments that help organizations identify, prioritize, and mitigate risks effectively.
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, breached accounts, phishing addresses, and content on the dark web, ensuring comprehensive coverage.
Is Threat Watch suitable for small businesses?
Absolutely. Threat Watch is designed for organizations of all sizes, providing essential cybersecurity insights that are crucial for small businesses looking to protect their digital assets.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch can be integrated with various cybersecurity tools and platforms, enhancing the overall security ecosystem and allowing for a more coordinated approach to threat management.
Alternatives
Pursuit Alternatives
Pursuit is an AI-powered intelligence platform designed specifically for businesses targeting the public sector, particularly state, local, and educational government entities. By analyzing data from over 90,000 public entities, Pursuit helps users identify actionable opportunities, allowing sales teams to engage proactively with decision-makers. Users often seek alternatives to Pursuit due to various factors, including pricing, specific feature sets, or unique platform requirements that better align with their organizational needs. When searching for an alternative, it's essential to consider aspects such as data accuracy, user experience, integration capabilities, and the comprehensiveness of market insights to ensure the chosen platform meets their strategic goals effectively.
Threat Watch Alternatives
Threat Watch is an innovative cybersecurity intelligence solution that falls under the business intelligence category, enabling organizations to assess and manage their cyber health effectively. Users often seek alternatives for various reasons, including pricing considerations, specific feature requirements, or the need for compatibility with particular platforms. When selecting an alternative, it's essential to consider factors such as the range of features offered, the ease of use, customer support, and how well the solution integrates with existing systems to ensure comprehensive protection against cyber threats.
