iGPT vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
iGPT transforms messy email data into instant, secure, context-aware answers for enterprise agents and workflows.
Last updated: March 1, 2026
Threat Watch
Quickly assess your cybersecurity health with Threat Watch's insights on compromised accounts and potential threats.
Last updated: March 1, 2026
Visual Comparison
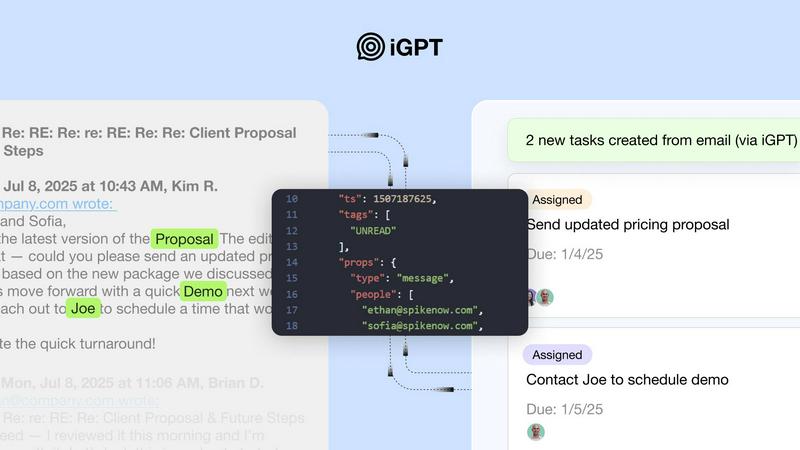
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT features a live playground and SDK for developers to quickly test requests and responses. This immediate integration capability ensures that enterprises can start leveraging the power of email intelligence without extensive setup or delay, enhancing productivity right from the start.
Contextual Responses
When users send a request, iGPT provides responses that are ready for reasoning and automation. Each answer is not only relevant but also includes citations to the source, allowing users to trace back to the original email threads and attachments for verification and deeper understanding.
Hybrid Retrieval
iGPT combines semantic and keyword-based retrieval within a single call, employing advanced filtering and scoring techniques. This hybrid approach allows it to adapt to varying queries and extract the most pertinent information from extensive and complex email data, significantly improving response relevance and accuracy.
Continuous Data Indexing
With real-time ingestion, iGPT continuously indexes new messages and attachments as they arrive. This feature ensures that the responses generated are always based on the most current data, maintaining an up-to-date repository of insights that users can rely on for timely decision-making.
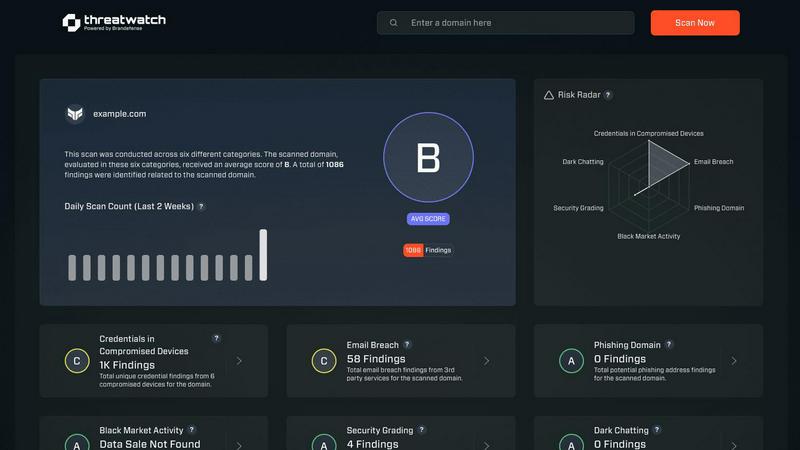
Threat Watch
Comprehensive Risk Assessment
Threat Watch provides a thorough evaluation of an organization’s cybersecurity posture by analyzing essential security categories. This feature allows users to identify potential weaknesses and prioritize remediation efforts based on the severity of identified risks.
Real-Time Insights
Stay ahead of cyber threats with Threat Watch's real-time insights. This feature continuously monitors the digital landscape, providing organizations with up-to-date information about emerging threats and vulnerabilities, enabling timely decision-making.
Automated Reporting
With advanced automation capabilities, Threat Watch generates detailed reports that summarize critical security findings. This feature streamlines the reporting process, making it easier for security teams to communicate risks and compliance status to stakeholders.
Dark Web Monitoring
Protect your organization's sensitive data with Threat Watch's dark web monitoring feature. This capability alerts users about compromised credentials and sensitive information that may be circulating on the dark web, allowing for swift action to secure assets.
Use Cases
iGPT
Email Assistants
iGPT empowers organizations to build intelligent email agents that can draft, prioritize, and take action on emails. By leveraging the full context of past communications, these agents enhance productivity and ensure that no critical tasks fall through the cracks.
Workflow Automation
Transforming email threads into actionable tasks, deadlines, and approvals is seamlessly achievable with iGPT. By flagging items that are stuck in the workflow, teams can proactively address bottlenecks and streamline their operations.
Support Copilots
Customer support teams can utilize iGPT to reconstruct the full customer story across long email chains, including attachments and shifts in tone. This contextual awareness enables representatives to provide more effective and personalized support to clients.
Compliance and Audit Trail
With iGPT, organizations can trace feedback, approvals, and rationale directly back to the original conversations. This comprehensive audit trail not only enhances compliance but also fosters accountability and transparency within teams.
Threat Watch
Identifying Vulnerabilities
Organizations can utilize Threat Watch to conduct regular assessments of their network and systems, identifying vulnerabilities before they can be exploited by cybercriminals. This proactive approach enhances overall security posture.
Incident Response Planning
In the event of a security incident, Threat Watch provides valuable intelligence that aids in incident response planning. Security teams can analyze compromised accounts and phishing attempts to develop strategies to mitigate future risks.
Cyber Hygiene Maintenance
Regular scans with Threat Watch help organizations maintain cyber hygiene by continuously monitoring for compromised credentials and vulnerabilities. This ongoing vigilance is essential for sustaining a secure digital environment.
Compliance Assurance
For organizations subject to regulatory requirements, Threat Watch assists in maintaining compliance by providing insights into security vulnerabilities and breaches. This feature ensures that businesses can demonstrate their commitment to cybersecurity best practices.
Overview
About iGPT
Imagine a world where the rich, contextual intelligence embedded within your organization's emails and communications is not only accessible but also actionable. iGPT is an enterprise-grade API that serves as a secure and intelligent gateway for AI agents and workflows, designed specifically for developers and enterprises. It transforms the chaotic landscape of email threads, attachments, and conversations into trusted, context-aware answers that drive meaningful action. By eliminating the traditional bottlenecks of AI integration—such as complex parsing and maintaining fragile prompt chains—iGPT offers a unified endpoint. This single natural language query can trigger a sophisticated pipeline that manages real-time retrieval, context shaping, and reasoning. With iGPT, teams can confidently deploy systems for sales, customer success, compliance, and beyond, ensuring that every response is grounded in source data while maintaining enterprise-grade security and full auditability. iGPT not only reads emails; it comprehensively understands the narratives within, turning communication data into a strategic asset that propels organizations forward.
About Threat Watch
Threat Watch is a sophisticated cybersecurity intelligence solution designed to empower organizations by providing them with a clear understanding of their cyber health. This innovative tool meticulously evaluates a multitude of critical security categories, such as compromised credentials, breached accounts, phishing addresses, and dark web content. By presenting a unified view of an organization’s assets, vulnerabilities, and exposures, Threat Watch enables IT professionals, security teams, and business leaders to swiftly identify and prioritize risks. The main value proposition lies in its ability to transform complex data into actionable intelligence, allowing businesses to mitigate risks faster and more effectively than ever before. With real-time insights and automated assessments, organizations can proactively safeguard their digital environments. Discover your cybersecurity health and fortify your defenses with Threat Watch, a crucial ally in the evolving landscape of cybersecurity threats.
Frequently Asked Questions
iGPT FAQ
How does iGPT ensure data security?
iGPT employs enterprise-grade protection at every layer, including zero data retention and role-based access control. Inputs, prompts, and outputs are processed in memory and are never stored, ensuring your data remains secure.
Can iGPT integrate with existing email systems?
Yes, iGPT is designed for easy integration with existing email systems. It automatically indexes emails and attachments, allowing organizations to leverage its capabilities without overhauling their current infrastructure.
What types of data can iGPT analyze?
iGPT can analyze a variety of data types found in emails, including text, attachments, and structured documents such as PDFs and spreadsheets. This broad capability enables comprehensive insights from diverse sources.
Is training on my data required for iGPT to function?
No, iGPT does not require training on your data to function effectively. Your data remains private and is not used for model training, ensuring that sensitive information is protected while still delivering valuable insights.
Threat Watch FAQ
How does Threat Watch improve cybersecurity?
Threat Watch improves cybersecurity by providing real-time insights and automated assessments that help organizations identify, prioritize, and mitigate risks effectively.
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, breached accounts, phishing addresses, and content on the dark web, ensuring comprehensive coverage.
Is Threat Watch suitable for small businesses?
Absolutely. Threat Watch is designed for organizations of all sizes, providing essential cybersecurity insights that are crucial for small businesses looking to protect their digital assets.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch can be integrated with various cybersecurity tools and platforms, enhancing the overall security ecosystem and allowing for a more coordinated approach to threat management.
Alternatives
iGPT Alternatives
iGPT is an enterprise-grade API designed to provide secure and instant answers from the often chaotic world of email data and attachments. It fits within the realm of business intelligence, acting as a sophisticated gateway for AI agents to extract meaningful insights from unstructured communication. Users typically seek alternatives to iGPT for various reasons, including pricing concerns, specific feature sets, or compatibility with existing platforms. When evaluating alternatives, it's essential to consider factors such as ease of integration, the comprehensiveness of data processing, and the level of security provided to ensure that your organization's sensitive information remains protected. As organizations increasingly rely on advanced AI solutions, finding the right tool that meets unique operational needs becomes paramount. A suitable alternative should offer a seamless user experience, robust data handling capabilities, and a clear understanding of context to maximize the value extracted from communication data. Additionally, evaluating the scalability and support options can help ensure the chosen solution aligns with long-term business objectives.
Threat Watch Alternatives
Threat Watch is an innovative cybersecurity intelligence solution that falls under the business intelligence category, enabling organizations to assess and manage their cyber health effectively. Users often seek alternatives for various reasons, including pricing considerations, specific feature requirements, or the need for compatibility with particular platforms. When selecting an alternative, it's essential to consider factors such as the range of features offered, the ease of use, customer support, and how well the solution integrates with existing systems to ensure comprehensive protection against cyber threats.
