Opal44 vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
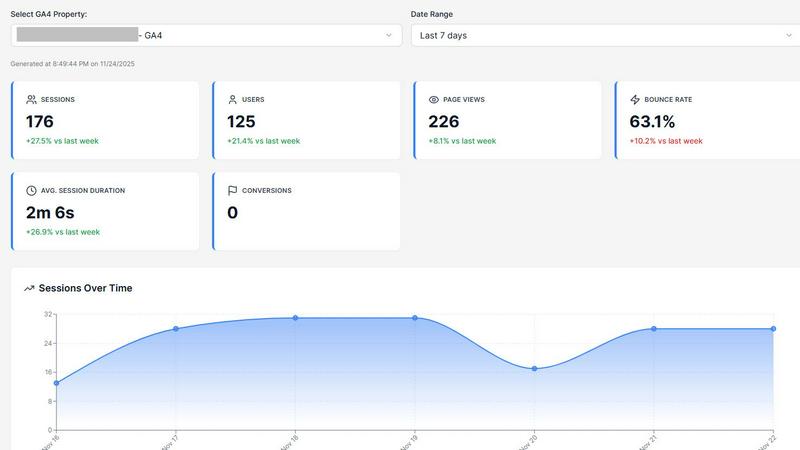
Discover what your website data truly means with plain English AI insights.
Last updated: March 4, 2026
Threat Watch
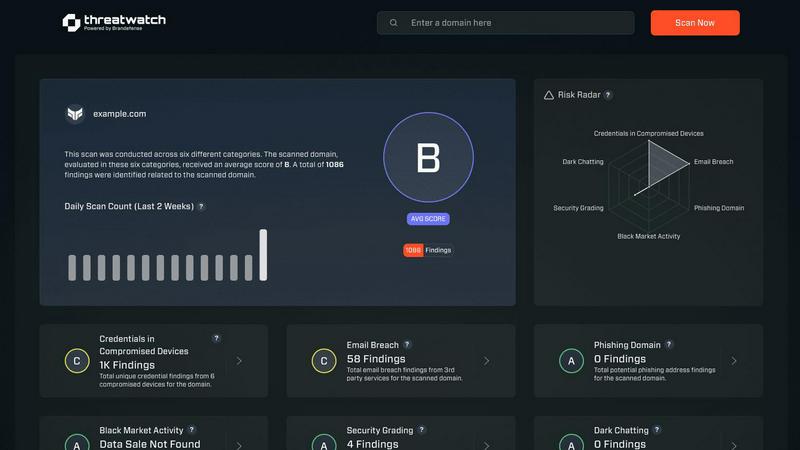
Quickly assess your cybersecurity health with Threat Watch's insights on compromised accounts and potential threats.
Last updated: March 1, 2026
Visual Comparison
Opal44
Threat Watch
Feature Comparison
Opal44
Plain English Insights Engine
This is the heart of Opal44. The AI doesn't just report numbers; it interprets your GA4 data and explains trends, anomalies, and performance in simple, everyday language. Instead of seeing "Sessions: -15% MoM," you'll get an insight like, "Your traffic from social media dipped this month, likely because your top-performing post from last month hasn't been replaced." It translates complex metrics into clear cause-and-effect explanations anyone can understand, making data accessible to every team member.
Conversational, Chat-Style Reporting
Forget static, intimidating reports. Opal44 delivers insights in a friendly, dialogue-based format that feels like you're chatting with a knowledgeable guide. This approach makes absorbing information natural and engaging. You can explore your data through simple questions and receive responses that build a coherent story about your website's health, encouraging a more curious and exploratory relationship with your analytics.
Smart, Actionable Recommendations
Beyond explaining the "what," Opal44 focuses on the "so what?" The AI analyzes your specific data patterns to provide tailored, data-driven tips. These aren't generic best practices; they are contextual suggestions, such as pointing out which high-traffic pages have low engagement and proposing content tweaks, or identifying a demographic segment that's converting highly and suggesting targeted campaigns.
Real-Time Performance Alerts
Stay proactively informed about significant changes without constantly monitoring dashboards. Opal44's alert system notifies you immediately of critical events like unexpected traffic spikes, sudden drops, or unusual conversion activity. This allows you to capitalize on opportunities or address issues as they happen, turning reactive data checking into proactive business management.
Threat Watch
Comprehensive Risk Assessment
Threat Watch provides a thorough evaluation of an organization’s cybersecurity posture by analyzing essential security categories. This feature allows users to identify potential weaknesses and prioritize remediation efforts based on the severity of identified risks.
Real-Time Insights
Stay ahead of cyber threats with Threat Watch's real-time insights. This feature continuously monitors the digital landscape, providing organizations with up-to-date information about emerging threats and vulnerabilities, enabling timely decision-making.
Automated Reporting
With advanced automation capabilities, Threat Watch generates detailed reports that summarize critical security findings. This feature streamlines the reporting process, making it easier for security teams to communicate risks and compliance status to stakeholders.
Dark Web Monitoring
Protect your organization's sensitive data with Threat Watch's dark web monitoring feature. This capability alerts users about compromised credentials and sensitive information that may be circulating on the dark web, allowing for swift action to secure assets.
Use Cases
Opal44
For Marketing Teams Needing Clear Reporting
Marketing teams can use Opal44 to cut through the complexity of GA4 and generate clear, jargon-free reports for stakeholders. Instead of presenting confusing charts, they can share straightforward narratives about campaign performance, audience behavior, and ROI, making strategy meetings more productive and decision-making faster and more aligned.
For Small Business Owners Managing Their Own Site
Small business owners and solo entrepreneurs who wear many hats can leverage Opal44 as their 24/7 analytics expert. It answers their pressing questions in plain terms: "Where is my best traffic coming from?" or "Is my new blog post working?" This empowers them to make confident, informed decisions about content, advertising, and site improvements without needing to hire a specialist.
For Digital Agencies Serving Clients
Agencies can use Opal44 to provide exceptional value to clients by translating complex data into understandable insights. They can create clear, conversational reports that clients actually read and comprehend, fostering trust and demonstrating tangible value. It simplifies communication and allows agencies to focus on strategy and execution rather than data explanation.
For Content Creators Optimizing Their Work
Bloggers, YouTubers, and content creators can connect Opal44 to understand their audience deeply. They can discover which topics resonate most, what time their audience is most active, or why a particular piece of content spiked in traffic. These plain-English insights guide content strategy, format experimentation, and publishing schedules to maximize reach and engagement.
Threat Watch
Identifying Vulnerabilities
Organizations can utilize Threat Watch to conduct regular assessments of their network and systems, identifying vulnerabilities before they can be exploited by cybercriminals. This proactive approach enhances overall security posture.
Incident Response Planning
In the event of a security incident, Threat Watch provides valuable intelligence that aids in incident response planning. Security teams can analyze compromised accounts and phishing attempts to develop strategies to mitigate future risks.
Cyber Hygiene Maintenance
Regular scans with Threat Watch help organizations maintain cyber hygiene by continuously monitoring for compromised credentials and vulnerabilities. This ongoing vigilance is essential for sustaining a secure digital environment.
Compliance Assurance
For organizations subject to regulatory requirements, Threat Watch assists in maintaining compliance by providing insights into security vulnerabilities and breaches. This feature ensures that businesses can demonstrate their commitment to cybersecurity best practices.
Overview
About Opal44
Have you ever stared at your Google Analytics 4 dashboard, feeling like you're deciphering an ancient code? You're not alone. Opal44 is a revolutionary AI-powered platform designed to bridge the gap between complex website data and genuine understanding. It transforms your raw GA4 metrics into clear, conversational insights delivered in plain English. Imagine simply asking, "Why did my traffic drop last Tuesday?" and receiving a straightforward, actionable answer instead of a confusing array of charts. This tool is crafted for business owners, marketers, content creators, and agency professionals who need to make data-driven decisions but lack the time or expertise to become analytics experts. Its core value proposition is profound simplicity: it demystifies your website's performance, turning overwhelming data into a clear narrative about what's working, what's not, and what you should do next. By connecting securely to your GA4 account in minutes, Opal44 acts as your personal data translator, empowering you to unlock the true story behind your traffic and conversions without the jargon.
About Threat Watch
Threat Watch is a sophisticated cybersecurity intelligence solution designed to empower organizations by providing them with a clear understanding of their cyber health. This innovative tool meticulously evaluates a multitude of critical security categories, such as compromised credentials, breached accounts, phishing addresses, and dark web content. By presenting a unified view of an organization’s assets, vulnerabilities, and exposures, Threat Watch enables IT professionals, security teams, and business leaders to swiftly identify and prioritize risks. The main value proposition lies in its ability to transform complex data into actionable intelligence, allowing businesses to mitigate risks faster and more effectively than ever before. With real-time insights and automated assessments, organizations can proactively safeguard their digital environments. Discover your cybersecurity health and fortify your defenses with Threat Watch, a crucial ally in the evolving landscape of cybersecurity threats.
Frequently Asked Questions
Opal44 FAQ
How does Opal44 connect to my data?
Opal44 connects to your Google Analytics 4 account using a secure, code-free, OAuth-based integration. This is a standard, read-only connection used by many marketing tools. You simply grant permission through Google's secure login, and Opal44 can access your aggregated data to generate insights. Your raw data never leaves Google's servers, and we never store personal identifiable information.
What is an "action" or "credit" in my plan?
An "action" or "credit" is consumed each time you ask Opal44's AI a question or generate an insight report. This includes asking conversational questions, generating summary reports, or receiving AI-powered recommendations. The system is designed to provide thoughtful, comprehensive answers per query. Your monthly plan includes a set number of credits to cover your exploratory needs.
Is my GA4 data safe with Opal44?
Absolutely. Data security and privacy are paramount. The connection is read-only, meaning Opal44 cannot alter any data in your GA4 account. We adhere to strict data protection protocols, never sell or share your data with third parties, and all data transmission is encrypted. You maintain complete ownership and control of your information at all times.
Can I use Opal44 with multiple GA4 properties?
Yes, but the capability depends on your chosen plan. The Starter plan supports one connected analytics account. The Professional plan allows for unlimited Google Analytics accounts at the property level, making it ideal for users managing multiple websites or client accounts. The Agency plan offers fully customizable setups for complex organizational needs.
Threat Watch FAQ
How does Threat Watch improve cybersecurity?
Threat Watch improves cybersecurity by providing real-time insights and automated assessments that help organizations identify, prioritize, and mitigate risks effectively.
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, breached accounts, phishing addresses, and content on the dark web, ensuring comprehensive coverage.
Is Threat Watch suitable for small businesses?
Absolutely. Threat Watch is designed for organizations of all sizes, providing essential cybersecurity insights that are crucial for small businesses looking to protect their digital assets.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch can be integrated with various cybersecurity tools and platforms, enhancing the overall security ecosystem and allowing for a more coordinated approach to threat management.
Alternatives
Opal44 Alternatives
Opal44 is an AI-powered business intelligence tool designed to demystify website analytics. It translates complex Google Analytics 4 data into simple, actionable insights using plain English, allowing users to ask questions and get clear answers without technical jargon. Users often explore alternatives for various reasons. Some may seek different pricing models or specific feature sets that better align with their workflow. Others might require integration with a broader suite of marketing tools or need more advanced, granular reporting capabilities beyond conversational insights. When evaluating other options, consider what truly matters for your team. Look for a solution that matches your comfort level with data, integrates seamlessly with your existing tech stack, and delivers insights in a format that leads to confident decision-making. The goal is to find a tool that turns data from a mystery into a clear guide for growth.
Threat Watch Alternatives
Threat Watch is an innovative cybersecurity intelligence solution that falls under the business intelligence category, enabling organizations to assess and manage their cyber health effectively. Users often seek alternatives for various reasons, including pricing considerations, specific feature requirements, or the need for compatibility with particular platforms. When selecting an alternative, it's essential to consider factors such as the range of features offered, the ease of use, customer support, and how well the solution integrates with existing systems to ensure comprehensive protection against cyber threats.
