CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
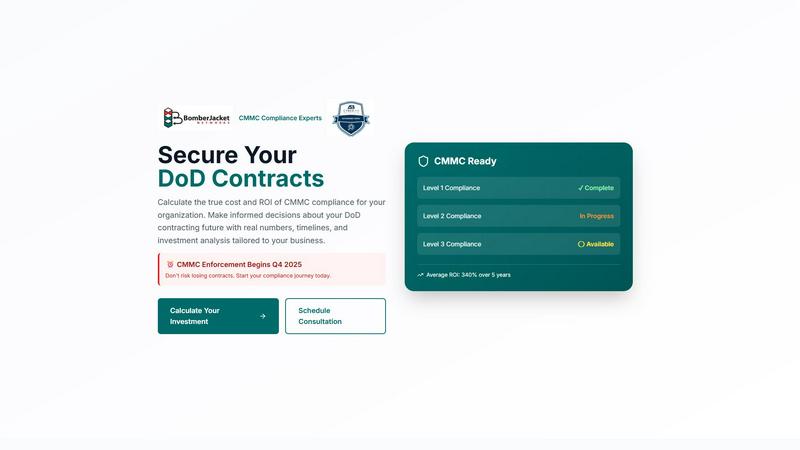
CMMC ROI
Unlock the true cost and ROI of CMMC compliance to secure your DoD contracts and future-proof your business.
Last updated: March 1, 2026
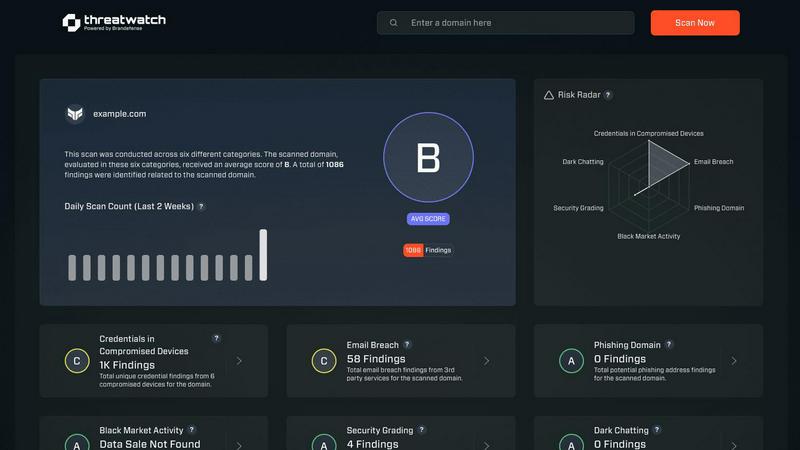
Threat Watch
Quickly assess your cybersecurity health with Threat Watch's insights on compromised accounts and potential threats.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Interactive Investment Calculator
The CMMC ROI calculator allows users to input specific business parameters to generate tailored financial projections. This ensures that each contractor receives an analysis that reflects their unique circumstances, making strategic planning far more accessible.
Multi-Year Financial Projections
This tool provides a comprehensive view of the financial implications of CMMC compliance over a five-year horizon. Users can view estimated costs, returns, and timelines, empowering them to make data-driven decisions.
Risk Assessment and Contract Protection
CMMC ROI quantifies the contract value at risk without certification, illustrating the potential financial loss contractors could face. This feature helps businesses understand the critical need for compliance to protect their revenue streams.
ROI and Payback Period Calculation
The tool calculates not only the expected ROI but also the timeline to break even on investments made for CMMC compliance. This feature allows contractors to see the financial benefits of compliance in a clear, concise format.
Threat Watch
Comprehensive Risk Assessment
Threat Watch provides a thorough evaluation of an organization’s cybersecurity posture by analyzing essential security categories. This feature allows users to identify potential weaknesses and prioritize remediation efforts based on the severity of identified risks.
Real-Time Insights
Stay ahead of cyber threats with Threat Watch's real-time insights. This feature continuously monitors the digital landscape, providing organizations with up-to-date information about emerging threats and vulnerabilities, enabling timely decision-making.
Automated Reporting
With advanced automation capabilities, Threat Watch generates detailed reports that summarize critical security findings. This feature streamlines the reporting process, making it easier for security teams to communicate risks and compliance status to stakeholders.
Dark Web Monitoring
Protect your organization's sensitive data with Threat Watch's dark web monitoring feature. This capability alerts users about compromised credentials and sensitive information that may be circulating on the dark web, allowing for swift action to secure assets.
Use Cases
CMMC ROI
Small Defense Contractors
A small defense contractor with limited resources can use CMMC ROI to assess the costs associated with achieving Level 2 compliance. By understanding the investment required and potential returns, they can allocate budget effectively and secure necessary funding.
Medium-Sized Enterprises
Medium-sized companies can leverage CMMC ROI to evaluate their current compliance status and develop a strategic plan for CMMC certification. This proactive approach can enhance their competitive edge in bidding for DoD contracts.
Large Prime Contractors
For large prime contractors, CMMC ROI offers a detailed financial analysis of the substantial investments required for Level 3 compliance. By identifying the payback period and potential ROI, these firms can justify expenditures to stakeholders.
Technology Firms Supporting DoD
Technology firms that provide services to the DoD can utilize CMMC ROI to demonstrate the financial benefits of compliance to potential clients. This can enhance their marketability and increase win rates in competitive bidding scenarios.
Threat Watch
Identifying Vulnerabilities
Organizations can utilize Threat Watch to conduct regular assessments of their network and systems, identifying vulnerabilities before they can be exploited by cybercriminals. This proactive approach enhances overall security posture.
Incident Response Planning
In the event of a security incident, Threat Watch provides valuable intelligence that aids in incident response planning. Security teams can analyze compromised accounts and phishing attempts to develop strategies to mitigate future risks.
Cyber Hygiene Maintenance
Regular scans with Threat Watch help organizations maintain cyber hygiene by continuously monitoring for compromised credentials and vulnerabilities. This ongoing vigilance is essential for sustaining a secure digital environment.
Compliance Assurance
For organizations subject to regulatory requirements, Threat Watch assists in maintaining compliance by providing insights into security vulnerabilities and breaches. This feature ensures that businesses can demonstrate their commitment to cybersecurity best practices.
Overview
About CMMC ROI
CMMC ROI is an innovative and interactive investment calculator tailored for defense contractors navigating the complex landscape of Cybersecurity Maturity Model Certification (CMMC). Designed specifically for organizations working with the Department of Defense (DoD), this tool provides a clear financial roadmap that transforms the intimidating question of compliance costs into a comprehensive analysis of potential returns on investment. By allowing users to input unique business variables such as company size, DoD revenue, and current compliance status, CMMC ROI generates personalized, multi-year financial projections. This not only clarifies the estimated costs involved in achieving compliance but also highlights the potential payback period, five-year ROI, and the contract values at risk without CMMC certification. As DoD enforcement approaches in late 2025, CMMC ROI serves as an essential resource for contractors of all sizes to make informed decisions about their place in the defense industrial base.
About Threat Watch
Threat Watch is a sophisticated cybersecurity intelligence solution designed to empower organizations by providing them with a clear understanding of their cyber health. This innovative tool meticulously evaluates a multitude of critical security categories, such as compromised credentials, breached accounts, phishing addresses, and dark web content. By presenting a unified view of an organization’s assets, vulnerabilities, and exposures, Threat Watch enables IT professionals, security teams, and business leaders to swiftly identify and prioritize risks. The main value proposition lies in its ability to transform complex data into actionable intelligence, allowing businesses to mitigate risks faster and more effectively than ever before. With real-time insights and automated assessments, organizations can proactively safeguard their digital environments. Discover your cybersecurity health and fortify your defenses with Threat Watch, a crucial ally in the evolving landscape of cybersecurity threats.
Frequently Asked Questions
CMMC ROI FAQ
What is CMMC ROI?
CMMC ROI is an investment calculator designed to help defense contractors understand the financial implications of achieving Cybersecurity Maturity Model Certification (CMMC) compliance.
How does the ROI calculation work?
The ROI is calculated by comparing the protected value of DoD contracts against the total investment made for compliance. This includes implementation costs, maintenance, and recertification expenses.
Can CMMC ROI accommodate different company sizes?
Yes, CMMC ROI is tailored for defense contractors of all sizes, from small businesses to large prime contractors. Users can input their specific business metrics to receive personalized results.
What happens if I don't achieve CMMC compliance?
Without CMMC compliance, contractors face significant risks, including the potential loss of DoD contracts and the financial fallout from breaches or false claims, which can average around $2.5 million in costs.
Threat Watch FAQ
How does Threat Watch improve cybersecurity?
Threat Watch improves cybersecurity by providing real-time insights and automated assessments that help organizations identify, prioritize, and mitigate risks effectively.
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, breached accounts, phishing addresses, and content on the dark web, ensuring comprehensive coverage.
Is Threat Watch suitable for small businesses?
Absolutely. Threat Watch is designed for organizations of all sizes, providing essential cybersecurity insights that are crucial for small businesses looking to protect their digital assets.
Can Threat Watch integrate with other cybersecurity tools?
Yes, Threat Watch can be integrated with various cybersecurity tools and platforms, enhancing the overall security ecosystem and allowing for a more coordinated approach to threat management.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a cutting-edge tool designed to help defense contractors assess the financial implications of achieving compliance with the Cybersecurity Maturity Model Certification. As a business intelligence solution, it offers a personalized investment calculator that allows users to project costs and potential returns based on their unique company metrics. Users often seek alternatives due to factors such as pricing, specific feature requirements, or the need for compatibility with existing platforms. When exploring alternatives, it’s crucial to consider each option's ease of use, customization capabilities, and the depth of insights provided to ensure they meet your business needs.
Threat Watch Alternatives
Threat Watch is an innovative cybersecurity intelligence solution that falls under the business intelligence category, enabling organizations to assess and manage their cyber health effectively. Users often seek alternatives for various reasons, including pricing considerations, specific feature requirements, or the need for compatibility with particular platforms. When selecting an alternative, it's essential to consider factors such as the range of features offered, the ease of use, customer support, and how well the solution integrates with existing systems to ensure comprehensive protection against cyber threats.
